
eNews #2-2017: symbIoTe Software v1.1.0 Release

The fourth release of symbIoTe software has been published on GitHub on last Nov 16, tagged as version 1.1.0.
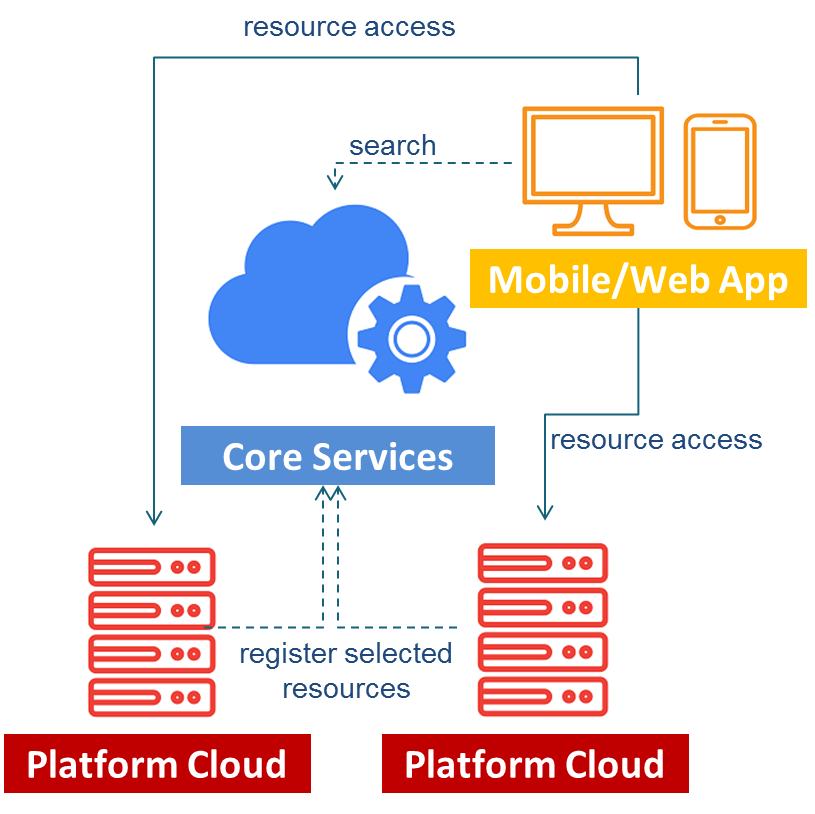
A new version of symbIoTe Core Services is included which fully implements a semantic IoT search engine over resources that are symbIoTe-enabled and offered by the underlying platforms. In addition, the developed symbIoTe Cloud Components extend existing IoT platforms with interoperability-related features. This release enables semantic interoperability and interactions between applications and platforms. In other words, it offers interoperability at the data level so that applications can search for appropriate resources using Core Services, understand resource metadata, while access to virtualized platform resources is enabled through a RESTful interface on the platform side.
- For more information on implemented concepts, read our blog post.
- For more information on steps you need follow to make your platform symbIoTe compliant with software version 1.1.0, read our blog post.
Release contents
Some key features included in this release are briefly highlighted here below.
Semantic Interoperability. Since symbIoTe targets primarily integration of existing platforms that use their own information models, our solution to semantic interoperability is flexible. We have defined a minimalistic Core Information Model (CIM) which defines the core IoT concepts (e.g., sensor, actuator, service), and each platform needs to conform to the CIM when describing their resources. However, since the CIM is minimalistic, symbIoTe specifies additional concepts for the Best Practice Information Model (BIM) which extends the CIM. Platforms can choose either to use the BIM when describing their resources, or can specify their own Platform-specific Information Model (PIM) which needs to extend the CIM.
symbIoTe’s Approach to AuthN & AuthZ. We have decoupled Authentication and Authorization, and rely on a PKI certificate trust chaining architecture and Multi-Domain Access Rights Composition in our solution. Resources are protected using the Attribute-Based Access Control (ABAC) paradigm where access policies are assigned to each resource, while attributes are distributed in standardized trusted data structures, i.e., JSON Web Tokens (JWT) and processed using a Mapping Function.
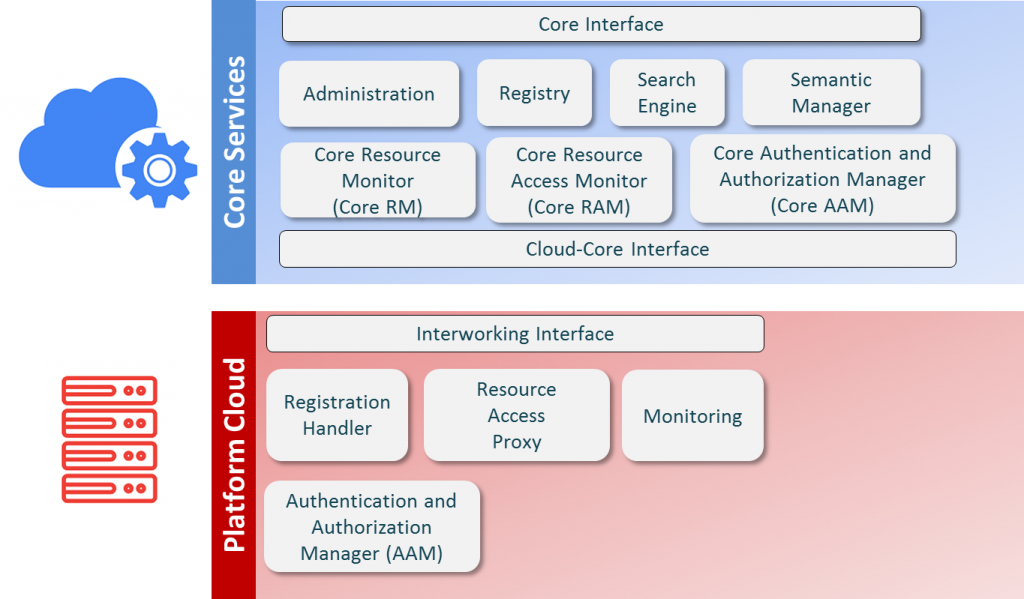
Core Services
We have enriched and consolidated a huge number of core services of the symbIoTe platform
- Administration to facilitate the control and administration of the symbIoTe Core Services by providing a web-based GUI.
- Registry to store data about registered resources offered to applications by using the supported information models.
- Search Engine to enable applications to find relevant resources registered within the Registry.
- Semantic Manager to store information models used within symbIoTe, verifies that a PIM extends the CIM, and verifies if resource metadata conforms to the information model it claims to be using.
- Core Resource Monitor (Core RM) to track availability of registered resources in order to ensure their availability. This will ensure that symbIoTe search results do not contain resources if their availability cannot be guaranteed.
- Core Resource Access Monitor (Core RAM) redirects applications to the actual resources offered by symbIoTe-enabled platforms. Additionally, it tracks information about resource popularity, i.e., which registered resources are being used by applications.
- Core Authentication and Authorization Manager (Core AAM) to ensure that trusted platforms register resources with symbIoTe, while mapping resource access rights to proper credentials. It implements ABAC-related procedures for the Core Services.
- Core Interface to grant northbound access (API) to symbIoTe Core Services by third parties (e.g., applications).
- Cloud-Core Interface to act as a gateway for accessing symbIoTe Core Services from the IoT platform’s side and symbIoTe platform-side components.
In other words, it provides endpoints for all components implementing the symbIoTe Core Service.
Cloud Platform
We also worked consistently on the symbIoTe cloud services, and specifically enriched:
- Registration Handler (RH) which enables platforms to register a selected set of resources to symbIoTe Core Services.
- Resource Access Proxy (RAP) which provides RESTful OData-like access to resources within a platform. Platforms need to implement a platform-specific RAP plugin to integrate its modules with symbIoTe.
- Monitoring which is used to monitor the status of resources and to record when applications access platform resources.
- Authentication and Authorization Manager (AAM) which implements the ABAC mechanism on the platform side.
This fourth software release comes after a challenging development process which our EU-wide team has followed in the last two years producing in total more than 90,000 LOC. Agile development process allowed us to incrementally release a number features over the last 9 months which implement a truly interoperable solution which currently integrates 5 real IoT platforms: Symphony by Nextworks, OpenIoT, openHAB, OpenUWEDAT by AIT and Node-RED.
Release history:
- Release 1 (Feb 2017): supported sensors exposed over OData-like REST-based interface on the platform side, basic registration and search features within Core Services.
- Release 2 (May 2017): supported actuators, basic security-related features for access control integrated on the platform side and within symbIoTe Core Services, platform-side monitoring.
- Release 3 (October 2017): included new features within Core Services: platforms can define their Platform-specific Information Model (PIM), verification that PIM extends the symbIoTe Core Information Model (CIM), ranking of search results; security-related features: 1) challenge-response procedure to verify authenticity of an application/component, 2) access policies are supported on the platform side to validate whether access to a specific resource should be granted or denied.
- Release 4 (November 2017): includes support for single-attribute access policies and filtering of search results according to access policies specified by platforms.


 This project has received funding from the European Union's Horizon 2020 research and innovation programme under grant agreement No 688156
This project has received funding from the European Union's Horizon 2020 research and innovation programme under grant agreement No 688156